Qualcomm boot-chain security on modern Snapdragon devices is best understood as a shift in trust boundaries rather than a single bug story. This deep-dive examines how boot-chain evolution, service-mediated unlock-state handling, the role of GBL as a UEFI application, and incomplete secure-boot enforcement can intersect on recent targets.
The strongest takeaway is architectural: on modern Qualcomm devices, a temporary code-execution primitive in the right EL1 boot stage can matter more than direct raw storage access. That is a major change from older platforms. Once a custom EFI payload can execute through the GBL path, it may no longer be necessary to defeat every earlier boot stage. Enough control to invoke the same verified-boot state machinery that legitimate firmware already uses can already be decisive.
- A central question is whether GBL, even if signed by Google, is independently validated by Qualcomm before execution.
- The wider technical context spans early Qualcomm boot chains, the UEFI transition, and the move from EL3-heavy research toward EL1-focused bootloader analysis.
- The key implication is that an unsigned GBL path plus access to Qualcomm verified-boot services can turn temporary boot-stage execution into a persistent unlock-state transition on certain modern devices.
1. Core technical claim
A simple but important observation drives this analysis: many public discussions about Qualcomm boot security focus on older parser bugs, transport bugs, or engineering-device behavior, while newer Android-based Qualcomm targets increasingly rely on UEFI-style loaders and additional boot components such as GBL. That changes the security question. Instead of asking only whether a classic boot component has a memory corruption issue, the more important question becomes whether the new execution path is correctly integrated into the chain of trust.
Two public clues make that question worth asking. First, older reports such as the XBL-loader ELF-header bug appeared either patched or less relevant to mainstream phones. Second, newer Qualcomm discussions identified GBL as a Google-signed UEFI application. That naturally raises a deeper question: does Qualcomm perform an independent signature validation step before a GBL payload executes, or has a new boot component been added without inheriting the full verification model of the rest of the chain?
The central thesis is straightforward: a newly added EFI execution path appears to have been integrated without equally strong signature enforcement, and that matters because modern unlock-state handling can be driven through trusted boot services from EL1.
2. Qualcomm boot-chain evolution across generations
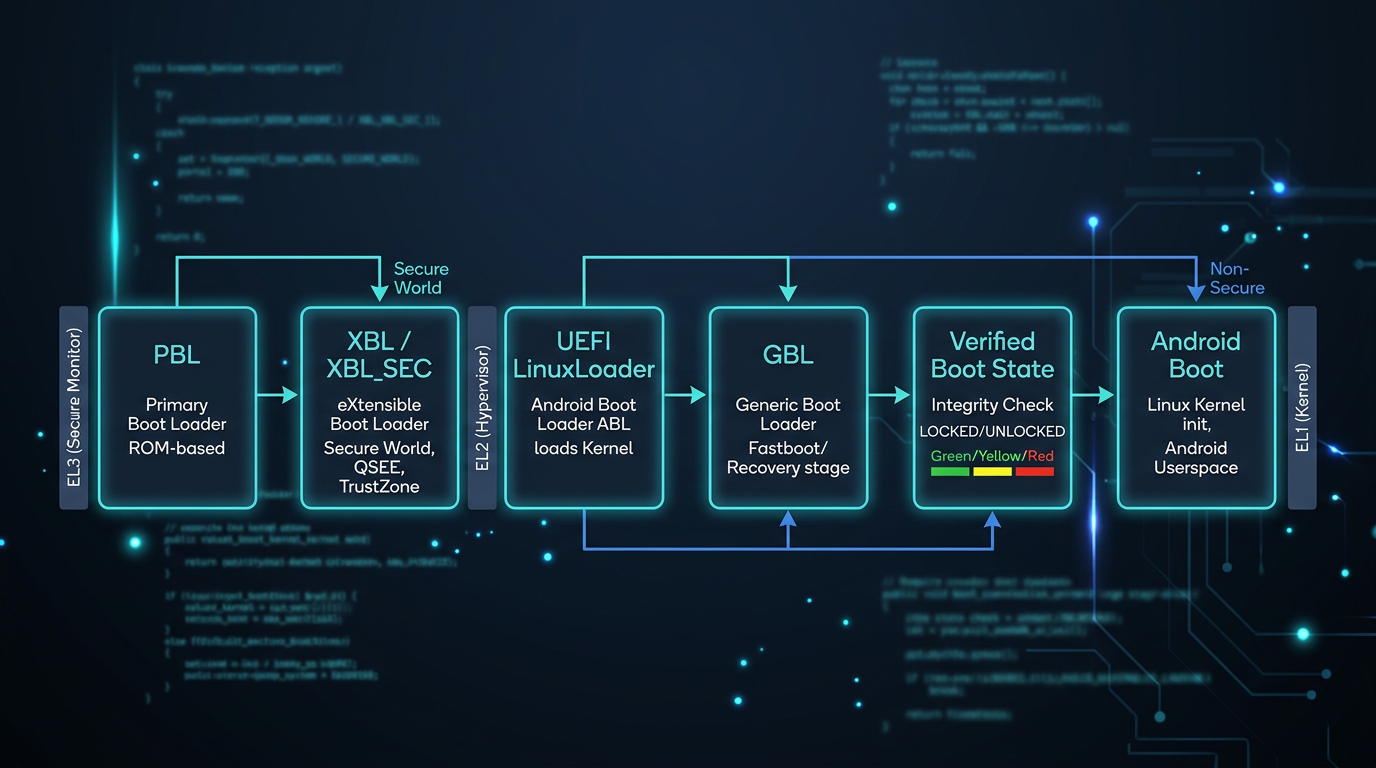
One reason this topic matters is that Qualcomm devices do not share a single security model. The history divides into multiple eras, and each era shifts the practical research surface.
| Era | Typical chain | Main privilege focus | Unlock-state model | Main lesson |
|---|---|---|---|---|
| Pre-835 | PBL -> SBL1 -> TZ/LK -> Kernel |
EL3-heavy | Often direct devinfo-style state |
Simple chain, fewer components, more direct control on unfused devices |
| 835 to SM8350 | PBL -> XBL/XBL_SEC -> ABL/LinuxLoader -> Android |
Mixed EL3 / EL2 / EL1 | Increasingly mediated by trusted services | UEFI adoption changes the attack surface and moves value upward |
| SM8250 and later hardening | PBL mitigations plus higher-layer focus | EL1 increasingly strategic | RPMB-backed and TEE-controlled | Temporary EL1 execution can still be decisive even when PBL is harder |
| Newer TME-era devices | PBL / TME separation | Distributed trust | Strongly mediated | Critical crypto and boot policy become more compartmentalized |
Pre-835: a simpler chain and a more direct security model
On pre-835 Qualcomm devices, the chain was easier to reason about. It was compact, PBL lived in Boot ROM, and the next major stages such as SBL1, TZ, and even firehose tended to run in high-privilege contexts. On unfused hardware, researchers could often gain broad control over later boot stages, dump ROM-adjacent content, and reason about the whole sequence with much less indirection than on newer platforms.
Older PBL implementations were also stricter than many people assume. When loading ELF-based boot content, Qualcomm verified hash segments, then validated the corresponding ELF headers and program headers before continuing. That made naive address changes or segment-level tampering much harder than public discussion sometimes suggested.
Early vulnerabilities and what they taught researchers
The historic firehorse era matters because it explains the mindset of earlier Qualcomm research. Old firehose builds exposed commands that effectively enabled arbitrary read/write behavior. Combined with MMU remapping tricks, researchers could hot-patch PBL-adjacent memory and re-enter code paths with modified validation logic. That work mattered not only because it was powerful, but because it showed how service-mode protocol bugs could become full boot-chain compromises.
A second older lesson is that unlock state could be much simpler on legacy devices. In some cases the bootloader lock state was effectively stored in a devinfo partition flag, so changing the right persistent field was enough. OEMs later hardened that path by migrating valuable state into RPMB or by requiring signed vendor-specific unlock material, as seen in Xiaomi’s older RSA-bound schemes.
835 to SM8350: the UEFI turn
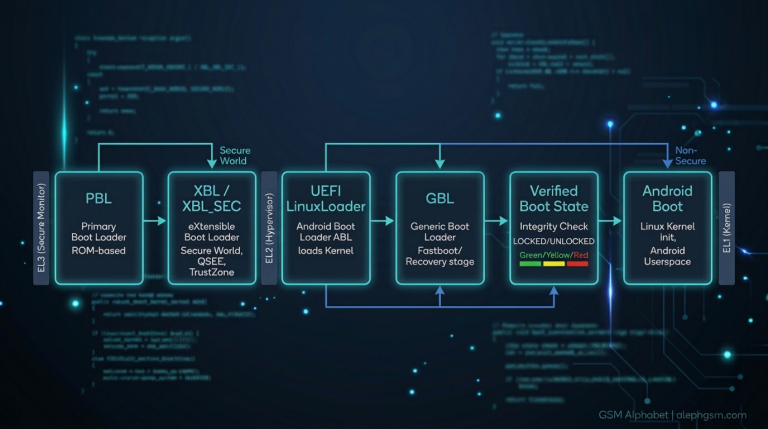
From Qualcomm 835 onward, the picture changes. PBL verifies and loads xbl and xbl_sec, with xbl_sec staying in EL3 while other components increasingly move to EL2 or EL1. Qualcomm also introduced a dual-signature model for some critical components such as xbl_sec and trust-zone-related content, reducing OEM freedom to arbitrarily replace those images.
At the same time, ABL and XBL became more UEFI-oriented. ABL still looks like ELF at a high level, but unpacking it with UEFITool reveals internal UEFI content, and the practical logic of interest is embedded inside LinuxLoader.efi. This shift is one reason later Qualcomm research begins to look more like firmware reverse engineering than classic bootloader patching.
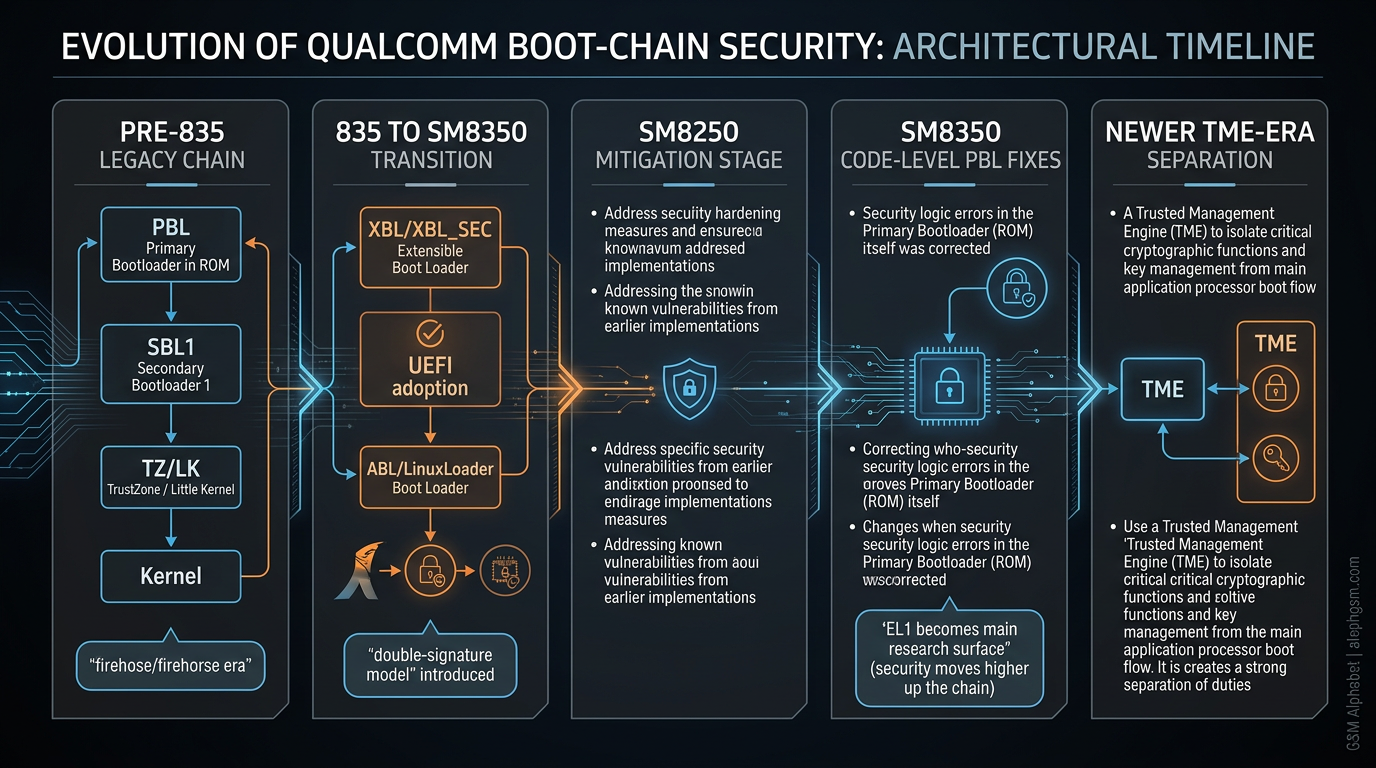
3. 9008, Sahara, Firehose, and why older service paths still matter
Before reaching GBL, it helps to revisit Qualcomm service mode because that history explains what was already known about reaching code execution lower in the chain. Qualcomm devices can enter 9008 through service combinations such as engineering wiring, key combos, magic values, or physical intervention. In that mode, PBL exposes the Sahara USB protocol to the host.
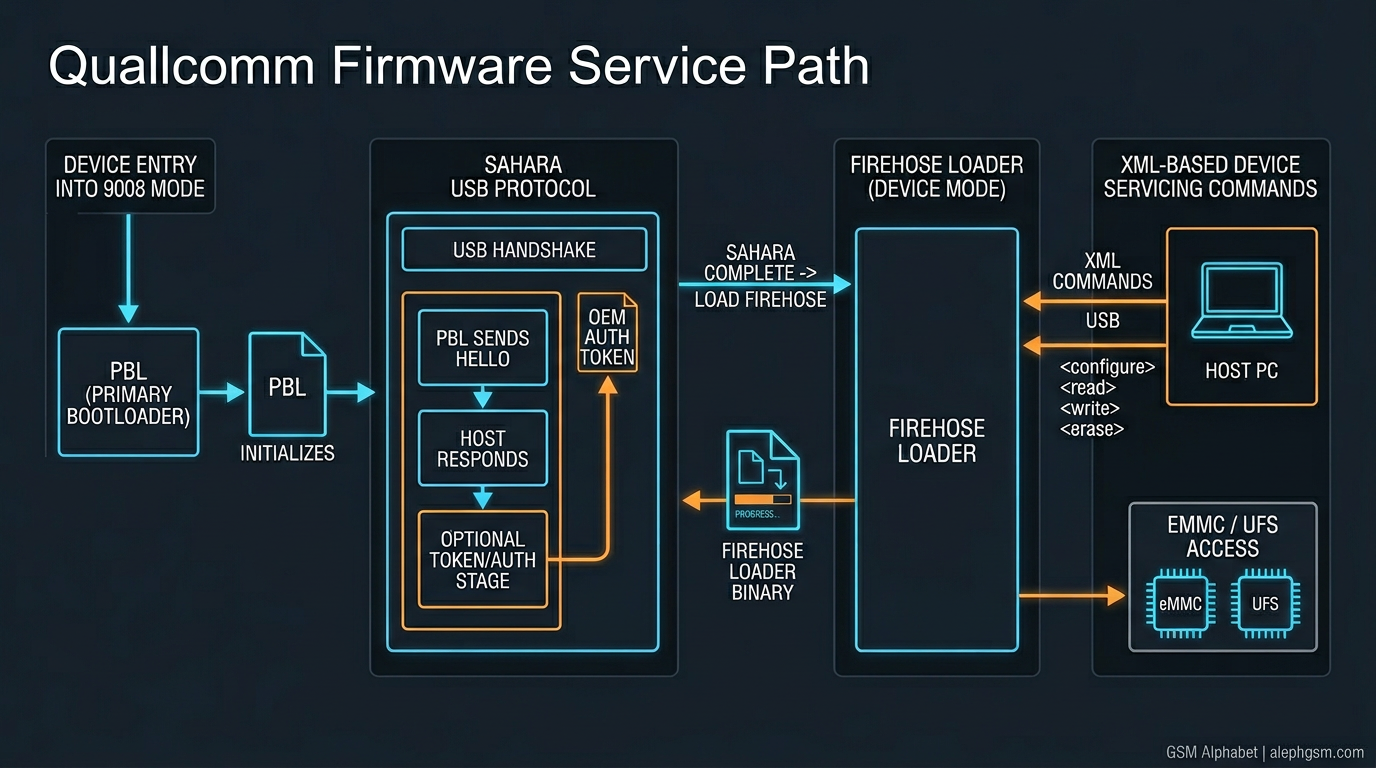
Sahara is used to initialize communication and transfer the next loader. Once a firehose image is accepted, the device exposes a much richer XML-based servicing environment for storage operations and diagnostics. OEMs can harden this path with their own authorization layers, including Xiaomi-style token flows where the device presents a challenge and the host must return a manufacturer-approved signature before privileged operations are allowed.
An older logic flaw in this ecosystem was that if a host never requested a token, the token buffer could remain at a default value, making the resulting signature reusable across devices that shared the same underlying assumptions. Variants of that logic reportedly persisted up to the Snapdragon 888 generation before vendors began explicitly rejecting signatures that were not preceded by a valid token-request phase.
The public Sahara recursion bug and why it still matters
A publicly described Sahara state-machine issue became especially interesting once Qualcomm’s PBL became 64-bit from the 835 generation onward. The vulnerable idea was not a classic parser overflow in isolation. It was a recursive control-flow problem: a state-reset command could re-enter the main Sahara handling routine in a way that repeatedly consumed stack space and moved the active stack toward adjacent data.
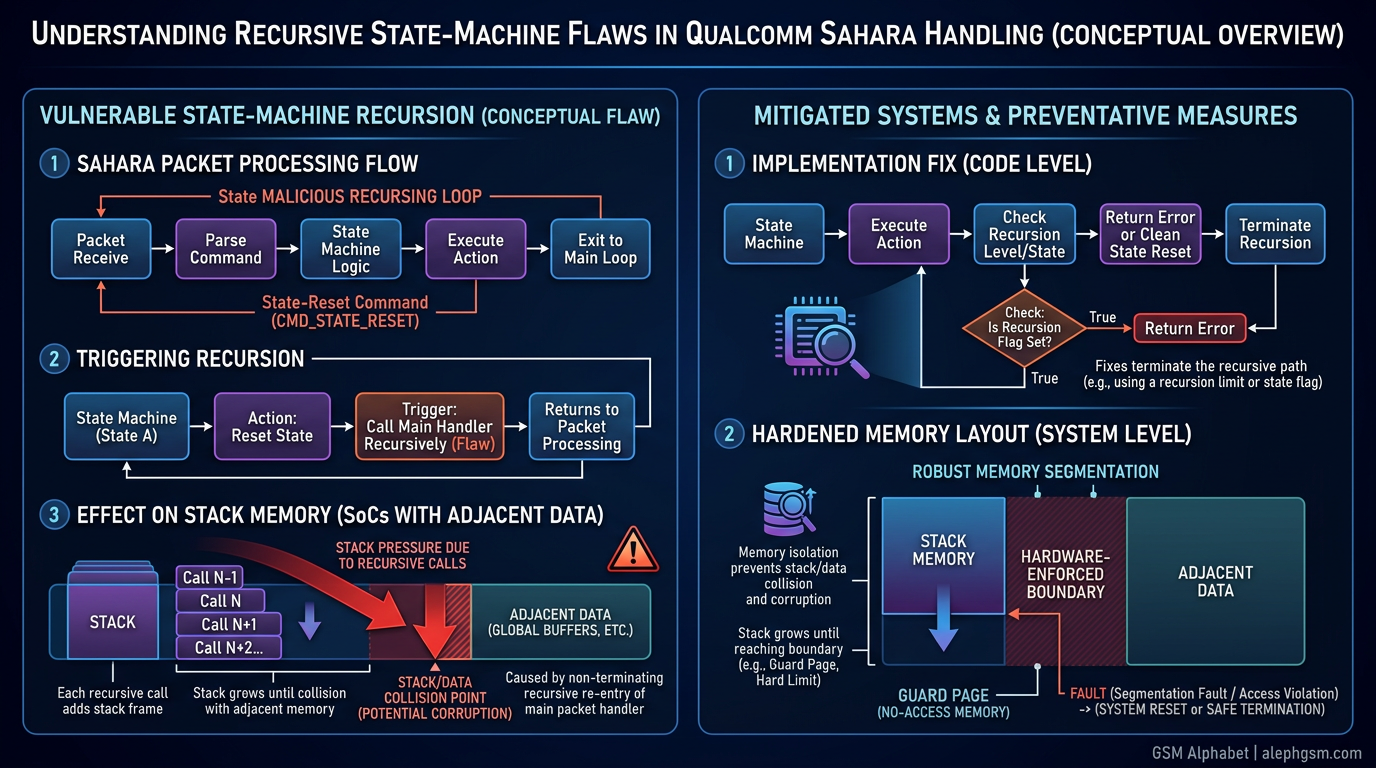
This was not universally exploitable. On Snapdragon 835, the memory layout above the stack was apparently not useful because invalid accesses crashed under MMU enforcement. On other SoCs such as 665, 710, 730, 845, and 855/855P, the memory layout was more interesting because adjacent data structures and indirect-call targets could sit within reach once recursion pushed the stack far enough.
Even then, the full path remained difficult in practice. Theoretical control over nearby data was only the beginning. Researchers still had to consider executable permissions, ROP-assisted MMU changes, xbl_sec loading details, UFS initialization, DRAM availability, and the fact that incorrect MMU setup could cause later trust-zone crashes. In other words, the historical lesson is not “PBL was easy to break,” but “older public bugs taught researchers how much real-world boot exploitation depends on memory layout, loader sequencing, and SoC-specific hardware conditions.”
The mitigation timeline is also important: SM8250-era devices reportedly hardened the stack-reset path through fuse-backed or implementation changes, and by SM8350 Qualcomm is described as having fixed the problem directly in PBL code. Later platforms also begin separating image-verification responsibilities into TME-style components, marking a new design phase.
4. Why EL1 becomes the practical research surface
After reviewing older EL3-focused history, the most important conceptual move is clear: for modern Qualcomm phones, the most practical target is often no longer trust-zone exploitation or pure PBL exploitation. Instead, EL1 becomes the high-value surface because that is where UEFI loaders, Android boot preparation, verified-boot service wiring, and vendor policy logic increasingly converge.
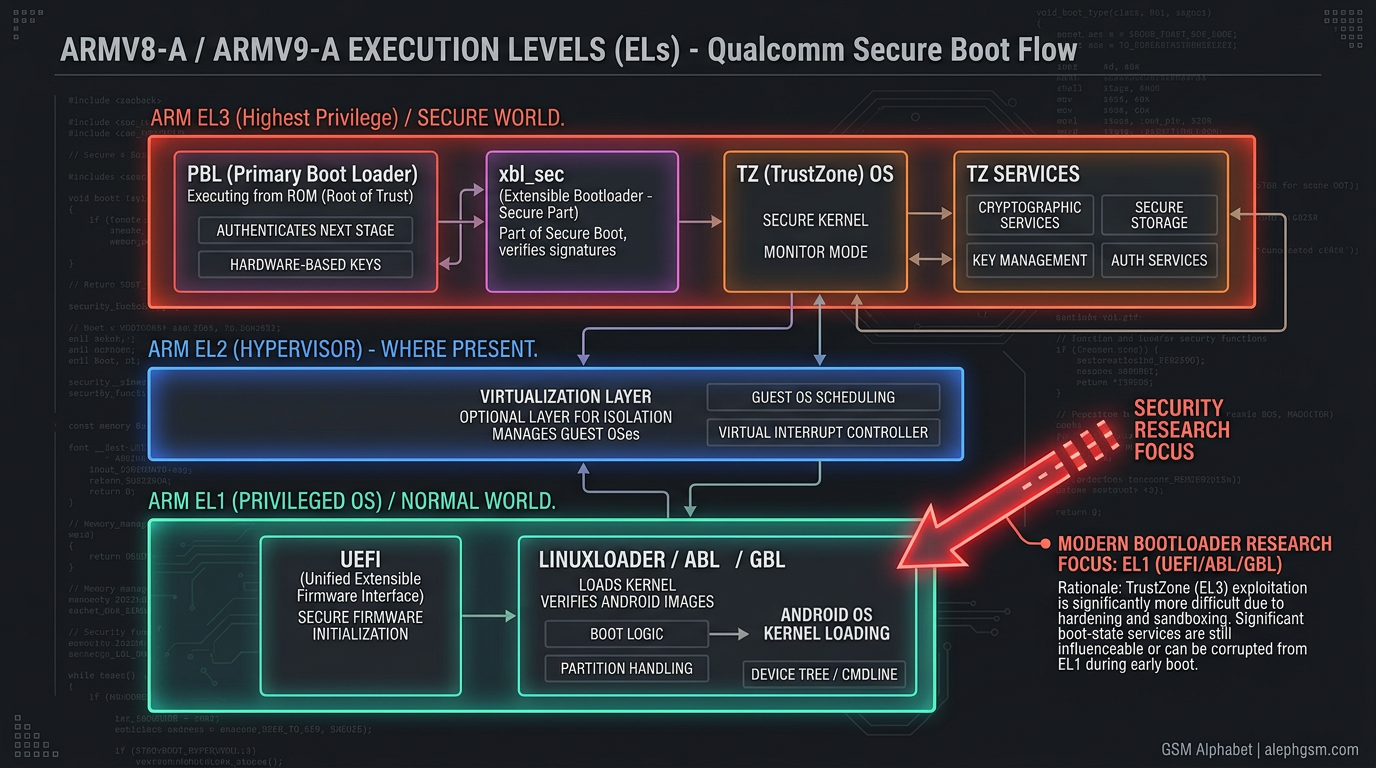
Direct trust-zone exploitation is technically possible in theory but much less practical in typical field conditions. Trusted services are often reached through SCM calls, require careful memory-boundary manipulation, and usually demand strong control from kernel or near-kernel contexts before meaningful privilege escalation can even begin. By contrast, if a UEFI-stage EL1 component can execute attacker-controlled code before Android finishes booting, that may already be enough to influence the persistent state transitions that matter.
This is also where Qualcomm’s design evolution becomes paradoxical. As OEM freedom over the lowest stages decreased, more logic moved into shared boot environments and protocol-driven service layers. That may reduce arbitrary image replacement, but it also makes any missing verification step in EL1 more strategically powerful.
5. Why GBL changes the research equation
GBL is best understood as a UEFI application introduced into newer Android boot flows, not merely as another opaque partition blob. That instantly generates a developer’s checklist of questions:
- From which partition is GBL loaded?
- How is a compatible UEFI app built for the target environment?
- Does the partition need a filesystem or any special container format?
- Is a signature check applied when the image is loaded?
- If signature verification exists, is it real Qualcomm enforcement or only generic UEFI logic that may be disabled?
- Which function ultimately writes unlock state on newer devices?
- Why must this happen in ABL/UEFI rather than from normal kernel space?
- If arbitrary UEFI apps can run, can they invoke the same trusted interfaces as the stock bootloader?
- Is the bootloader’s internal load address stable enough to call directly, or must researchers rely on protocol discovery?
This checklist is important because it turns a one-off observation into a reusable firmware-research methodology. Any developer analyzing a new Qualcomm UEFI path can apply the same exact questions.
6. Reverse engineering the GBL load path inside LinuxLoader
Answering those questions requires unpacking LinuxLoader.efi with UEFITool and tracing the code path responsible for GBL discovery. One of the most important findings is that GBL appears to be attempted unconditionally. The loader does not first consult a separate feature flag or other partition-stored enable bit. If GBL launch fails, normal boot continues, but the attempt is always made.
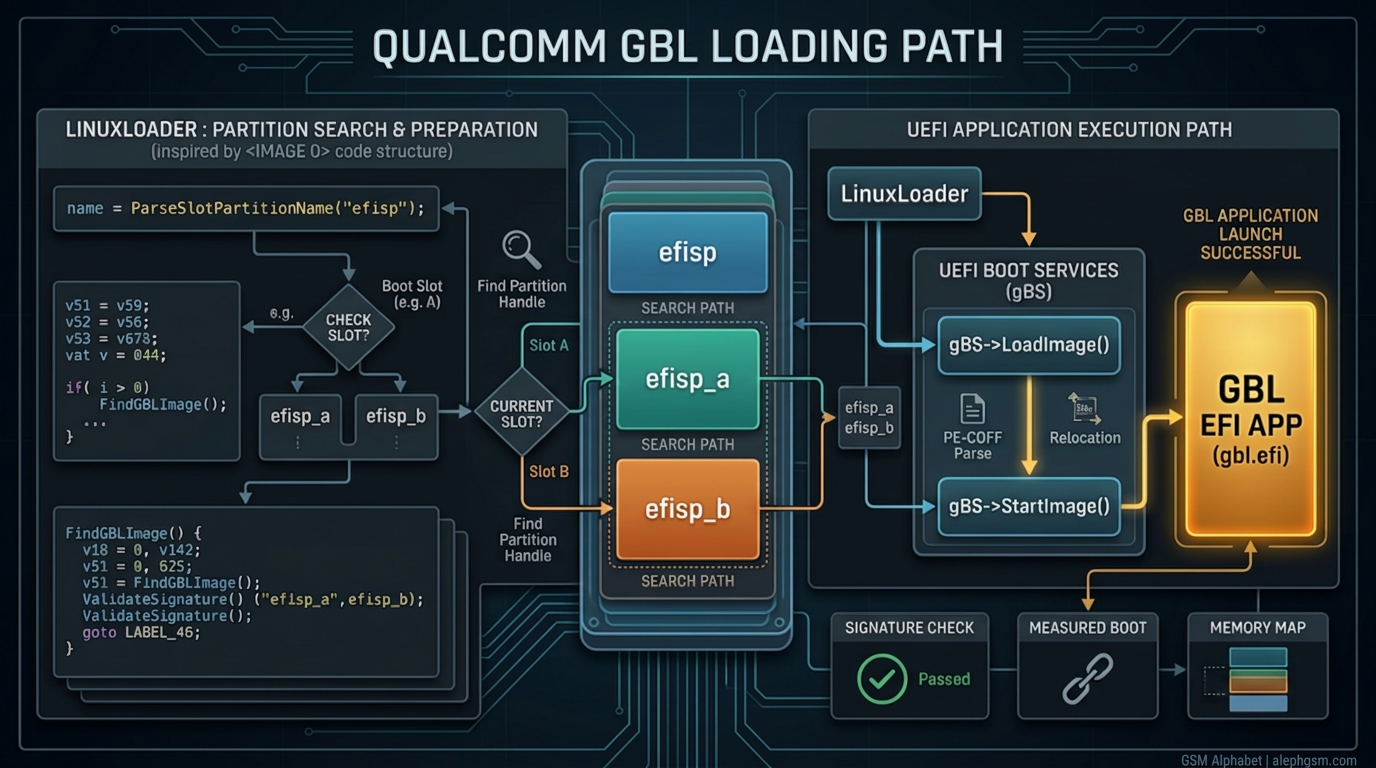
The next observation is the string evidence around efisp. The article infers that efisp, efisp_a, and efisp_b are candidate sources for the GBL payload. The associated helper resembles GetBlkIOHandles, which searches block devices by partition label, walking GPT or MBR metadata on non-removable media. That detail matters because it suggests the loader is not looking for a complex higher-level package format first. It is looking for a labeled storage source that can be resolved into an EFI device path.
Once the target handle is found, the path ultimately reaches standard boot services:
EFI_HANDLE LoadedImage = NULL;
EFI_STATUS Status;
Status = gBS->LoadImage(
FALSE,
ParentImageHandle,
DevicePathToGbl,
NULL,
0,
&LoadedImage
);
if (!EFI_ERROR(Status)) {
Status = gBS->StartImage(LoadedImage, NULL, NULL);
}Two subtle but useful implications follow. First, StartImage() returns to LinuxLoader after the EFI app exits, which means the stock boot environment remains the coordinator even when an extra EFI payload runs. Second, the relevant image does not appear to have a stable fixed load address in this flow; placement seems allocator-driven rather than statically hard-coded. That pushes the analysis away from direct internal function calls and toward protocol-based interaction.
7. Why UEFI Secure Boot may not be enforced here
This is the most important logic chain in the entire document. The analysis does not stop at “GBL uses LoadImage(), therefore it must be verified.” Instead, it asks a harder question: under what conditions does LoadImage() actually enforce signature validation in a Qualcomm UEFI build?
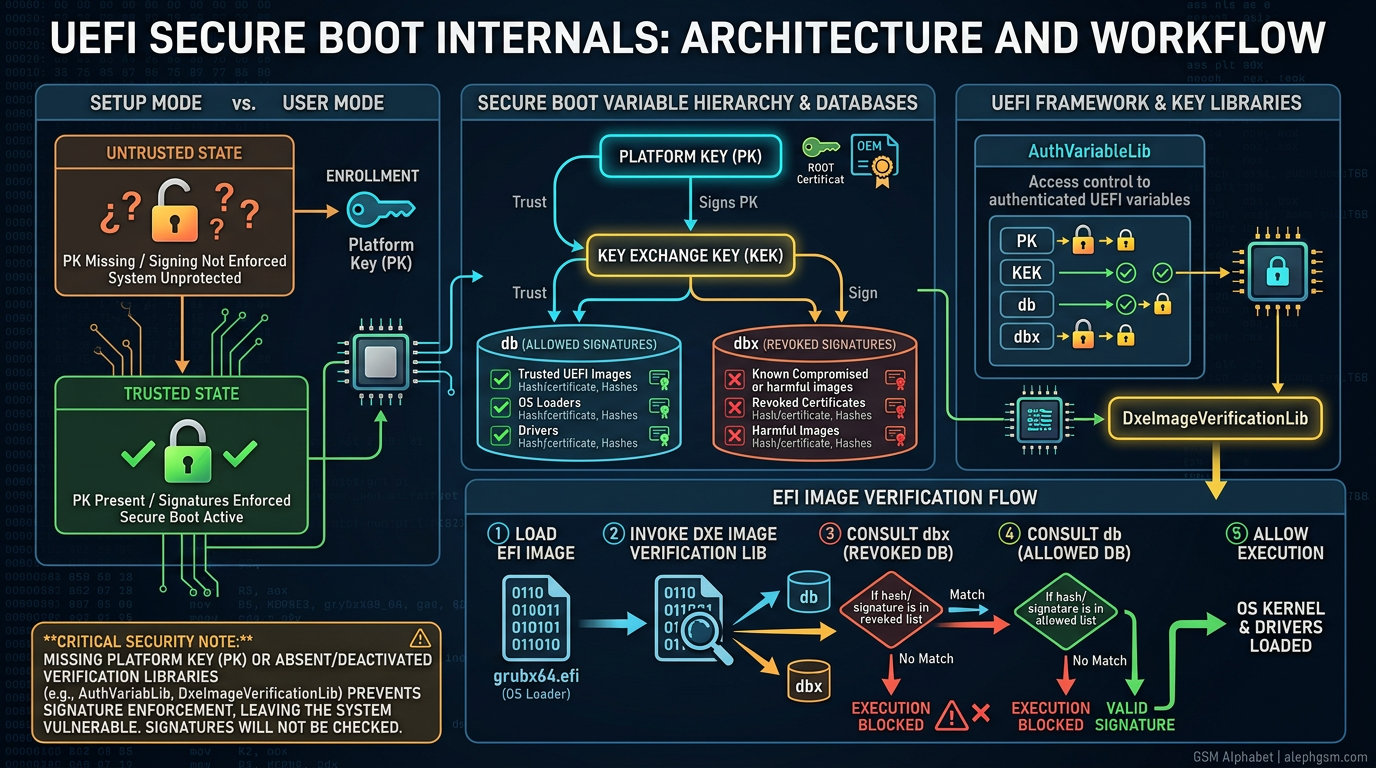
LoadImage() is not enough.In normal UEFI, EFI image verification depends on more than a single API call. The platform must have the right variable model, key enrollment state, trust databases, and verification libraries wired into the DXE/BDS path. In practical terms, several requirements matter:
- A valid platform key (
PK) must exist so the system transitions out of setup mode and into a user-mode secure-boot state. - Supporting key stores such as
KEK,db, anddbxmust exist so signatures can be validated and revoked content blocked. - Libraries such as
AuthVariableLibandDxeImageVerificationLibmust actually be present and referenced by the firmware build. - The target EFI image must be presented to that enforcement path, not merely passed through an API that can behave permissively when secure boot is inactive.
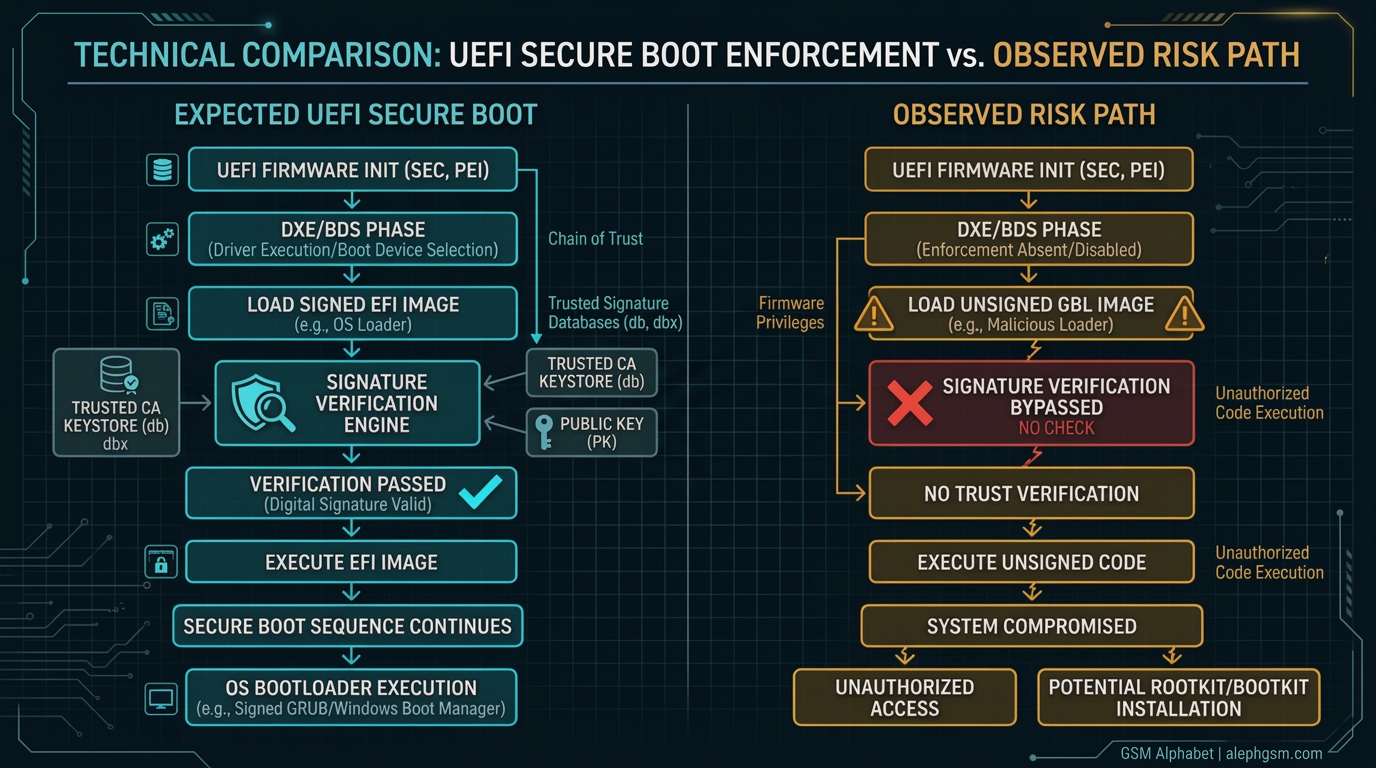
Several pieces of evidence point in that direction. LinuxLoader.efi itself appears to be loaded through the same generic boot-services model, yet analysis did not reveal an extra Authenticode-style signature in the way one would expect from a fully enforced secure-boot path. Older Qualcomm UEFI code also did not show obvious platform-key enrollment logic, and the relevant EDK2 verification libraries were not referenced in the build descriptions being inspected.
The resulting conclusion is that Qualcomm’s UEFI implementation on the tested class of targets appears not to have UEFI Secure Boot enabled for this path. If that conclusion is correct, an unsigned GBL payload is not blocked by EFI signature enforcement and can reach EL1 execution.
8. Unlock-state evolution: from raw flags to trusted services
Old “flip a lock bit” thinking no longer maps cleanly onto newer Qualcomm devices. On older devices, devinfo could directly hold the unlock state in a writable partition. On newer devices, the valuable state migrates into RPMB and becomes mediated by TEE-owned or firmware-owned interfaces. That means persistence is now a service problem, not just a storage problem.
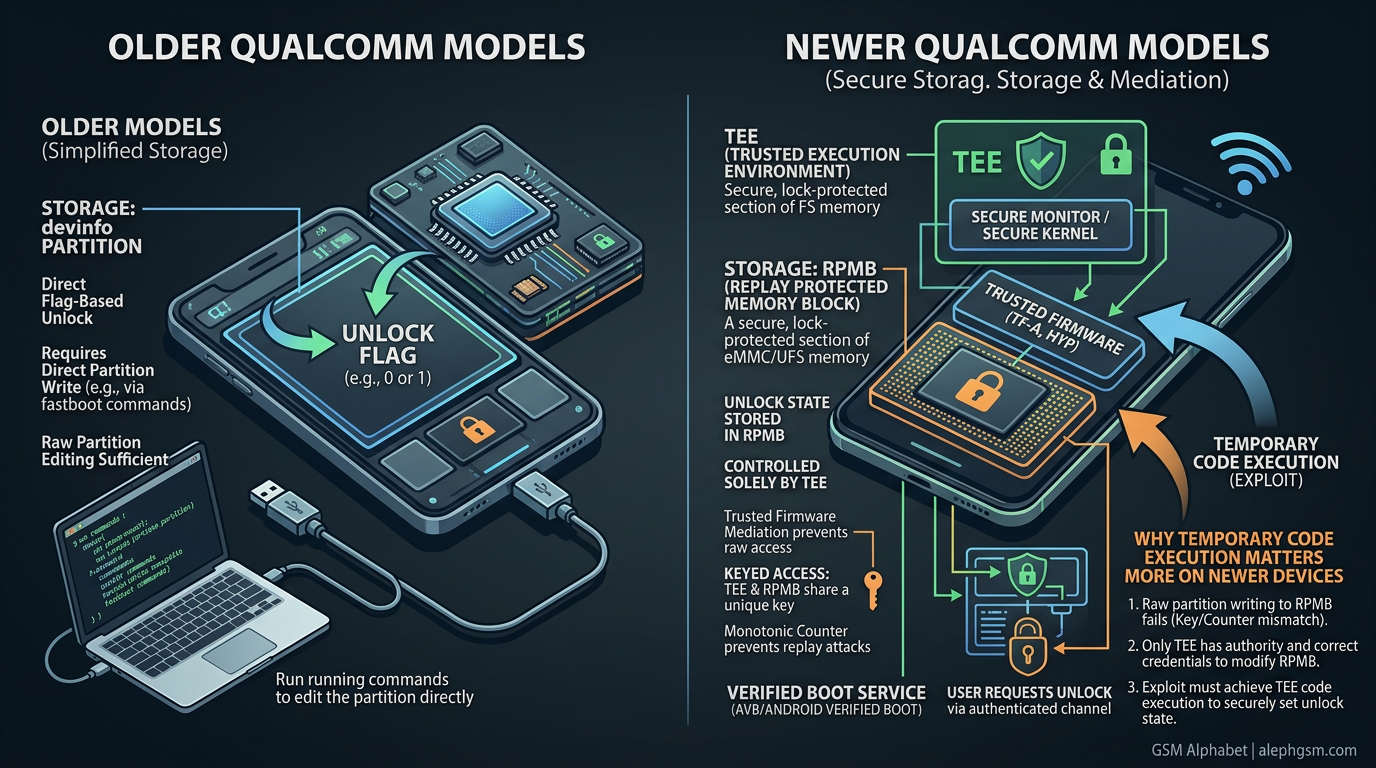
This is one of Qualcomm’s biggest architectural changes. Earlier research often tried to replace or bypass the entire chain. The modern insight is different: if trusted firmware already contains a legitimate routine that persists unlock state into secure storage, then temporary code execution in the correct boot context may be enough. You do not necessarily need to permanently replace the whole bootloader. You only need to invoke the same state-writing machinery the stock platform already trusts.
9. QCOM_VERIFIEDBOOT_PROTOCOL and why protocol discovery matters
Once direct raw editing becomes less useful, protocol discovery becomes central. The relevant UEFI logic calls into QCOM_VERIFIEDBOOT_PROTOCOL, specifically a member associated with VBRwDeviceState. This is discovered through gBS->LocateProtocol(), using a GUID to resolve the interface at runtime.
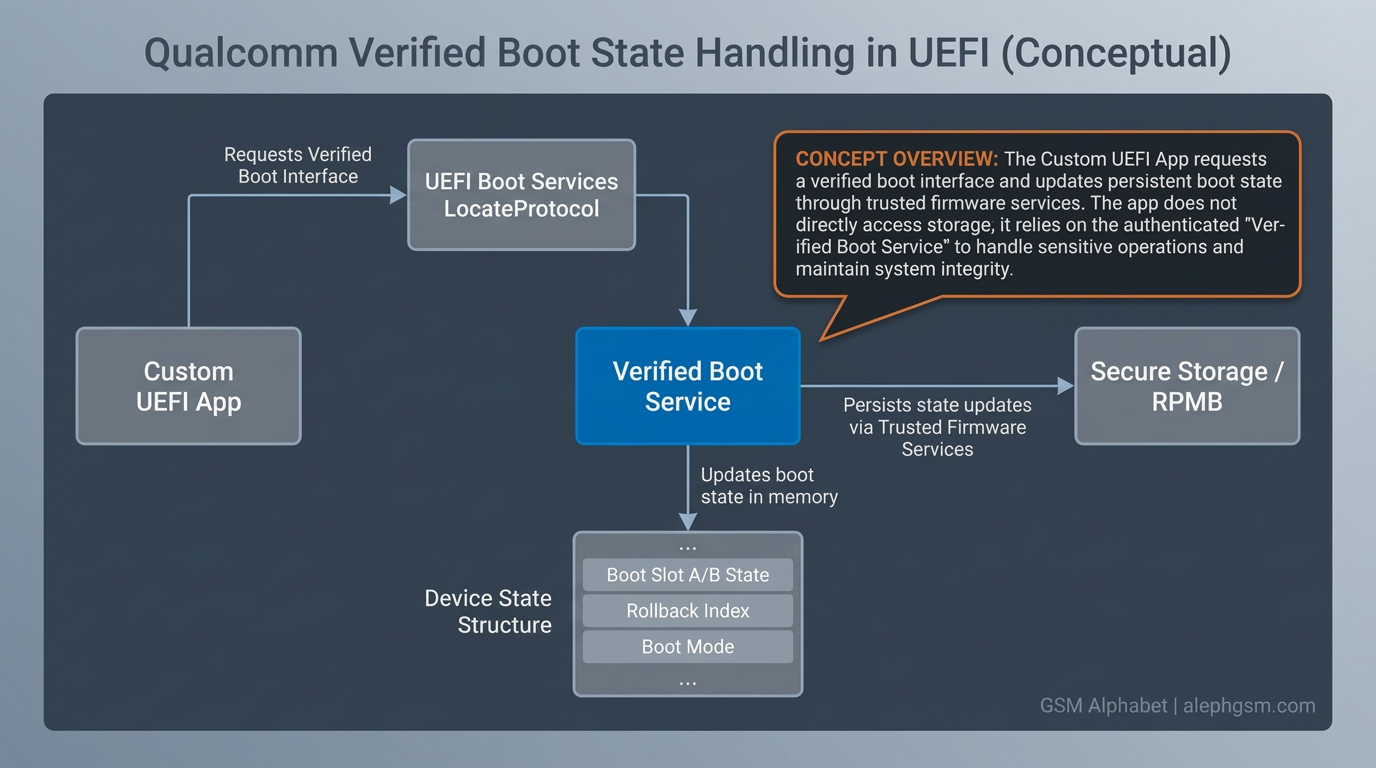
EFI_STATUS Status;
QCOM_VERIFIED_BOOT_PROTOCOL *VerifiedBoot = NULL;
Status = gBS->LocateProtocol(
&gEfiQcomVerifiedBootProtocolGuid,
NULL,
(VOID **)&VerifiedBoot
);
if (!EFI_ERROR(Status) && VerifiedBoot != NULL) {
/*
* Platform-specific verified-boot services mediate
* how boot state is read, updated, and persisted.
*/
}An important debugging lesson appears here. Treating the state as if one or two bytes were enough to flip the result does not work. The next lesson is that the state object is structured, includes magic and header validation, and cannot be safely modified as if it were an isolated boolean. On the tested target, the useful state blob was described as being roughly 3344 bytes long, and preserving that full serialized object while modifying only the intended fields was necessary to maintain validity.
This is a critical insight: on modern Qualcomm platforms, “unlock state” is not conceptually just a flag. It is part of a larger validated structure that participates in a trusted workflow. That alone explains why a custom UEFI app is more useful than a blind partition patch.
10. Why EL1 execution is enough to matter
A natural question is why the unlock-state write must happen during the ABL/UEFI stage instead of from the kernel later. The answer is not simply privilege level in the abstract. Both are privileged in different ways, but the boot-time environment has access to firmware protocols, service registration, and trusted interfaces that are not exposed in the same form once Android fully boots. That is why a temporary EL1 foothold in the bootloader environment can be more strategically useful than later userland or even conventional root.
In short: the firmware service exists, the protocol is already wired in, and the boot chain still trusts it. That is why the GBL path matters so much if signature enforcement on this route is missing.
11. Building and validating a custom UEFI application
Reverse engineering alone is not enough. Practical validation requires building a small UEFI application inside Qualcomm’s EDK2-derived environment, placing it inside QcomTestPkg, adding a matching .inf file, and updating QcomPkg.dec so the verified-boot protocol header can be resolved correctly.
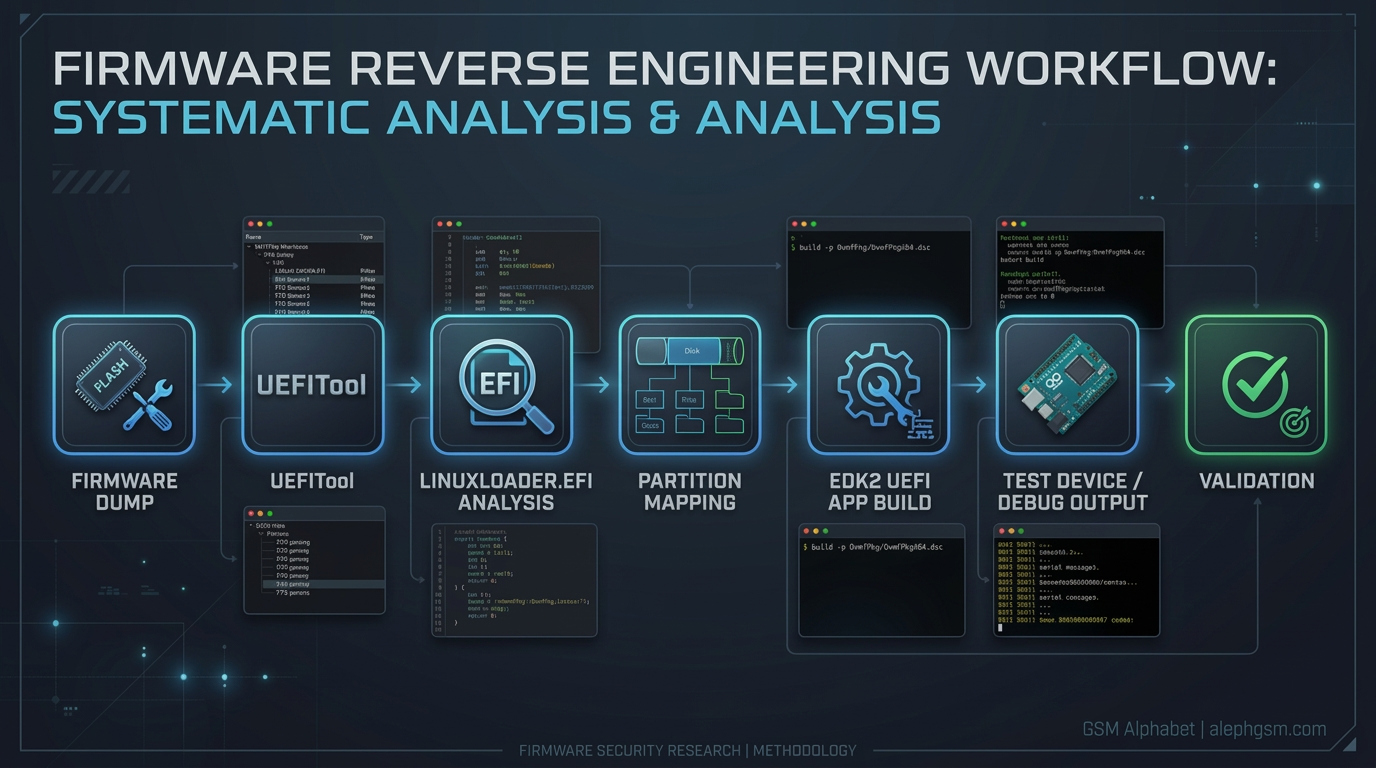
Linux also turns out to be a much better build environment than Windows for this task. The EDK2/BaseTools setup requires the usual environment variables plus a working AArch64 cross-compiler prefix and the PosixLike BaseTools path. The following build skeleton captures the idea:
export WORKSPACE=/path/to/edk2
export PYTHONPATH=$WORKSPACE/BaseTools/Source/Python
export EDK_TOOLS_PATH=$WORKSPACE/BaseTools
export PACKAGES_PATH=/path/to/edk2:/path/to/boot:/path/to/sdk:/path/to/ssg
export PATH=$PATH:$WORKSPACE/BaseTools/BinWrappers/PosixLike
export GCC49_AARCH64_PREFIX=aarch64-linux-gnu-
python3 edk2/BaseTools/Source/Python/build/build.py \
-p QcomPkg/QcomTestPkg/QcomTestPkg.dsc \
-a AARCH64 \
-b DEBUG \
-t GCC49 \
-m QcomPkg/QcomTestPkg/VbRwStateApp/VbRwStateApp.infTwo details are easy to miss but useful in practice. First, the -m switch is used to build only the target UEFI app rather than the full firmware tree. Second, missing include paths and BaseTools wrappers can cause repeated build errors until the environment is shaped to match Qualcomm’s boot-image tree expectations.
12. The efisp placement mistake that unlocked the whole path
One of the most practical and instructive points is the debugging mistake around efisp. Based on public GBL documentation from U-Boot-oriented environments, it is easy to assume that the partition would need a VFAT-style layout or some filesystem-aware placement scheme. That turns out to be the wrong mental model for the Qualcomm target being studied.
Because LinuxLoader was not passing a meaningful file path into a filesystem-based search flow, the target did not actually need a traditional VFAT arrangement. Instead, dropping the EFI payload into the efisp partition itself was enough for the loader to discover and run it. The harmless validation step was a trivial app that deliberately never returned; once the device stopped at that point instead of continuing normal boot, the loading hypothesis was effectively confirmed.
That debugging sequence matters for developers because it shows how easy it is to import the wrong assumptions from generic UEFI or U-Boot documentation. The right answer depends on the target’s actual loader implementation, not on what a different boot chain would normally do.
13. Claimed validation result on Snapdragon 8 Gen 5-class devices
After validating that a custom UEFI app can be reached, the harmless test can be replaced with one that interacts with verified-boot state handling. A demonstrated target is RedMagic 11, and the same logic has been claimed for other Snapdragon 8 Gen 5-era devices such as Xiaomi 17, Xiaomi 17 Pro, K90 Pro Max, and Nubia Z80, provided the necessary partition-write conditions exist.

The limitations are equally important. This is not a universal no-disassembly consumer unlock. The approach still depends on raw partition write access through 9008 or service workflows, programmer access, or hardware-assisted servicing. In other words, the biggest contribution here is the architectural path, not a turnkey public tool.
14. Why earlier generations and other vendors still matter
Qualcomm security remains generation-specific. Earlier SoCs have different practical exploit surfaces, including historical fastboot or ABL parser issues, old firehose weaknesses, and weaker storage models. Later SoCs harden PBL and push attackers upward. Some OEMs add their own unlock enforcement layers, including per-device signing schemes. Others rely more heavily on firmware policy and verified-boot service logic.
The GBL result is therefore not the only path that matters. On pre-8 Gen 5 devices, other vulnerabilities may still be the better route to full ABL control, kernel boot bypass, or unlock-state influence. Conversely, if an OEM preserves its own unlock workflow but still allows unsigned GBL-style execution, custom boot-policy logic could become possible there as well.
15. The full developer takeaway
For developers, firmware researchers, and OEM security teams, the main value lies in the model this analysis teaches:
- Do not analyze Qualcomm boot security as if every generation used the same trust boundaries.
- Treat EL1 boot stages as first-class security targets, not merely lower-value leftovers after PBL hardening.
- When a new component such as GBL is added, trace the real load path and do not assume secure boot is active just because generic UEFI APIs are present.
- Distinguish raw storage edits from protocol-mediated state transitions. On modern devices, trusted services often matter more than partitions.
- Validate with real build-and-run experiments. Static reverse engineering alone can suggest a path, but runtime behavior proves whether the path is live.
That is why this topic is more than a case study about a single device. It is a blueprint for how to audit any modern mobile boot chain that mixes vendor trust anchors, EDK2-derived loaders, Google-origin boot components, and secure-state services.
16. Public background and related reading
The broader public context includes several strands of work that help developers place this topic correctly:
- Aleph Security: Qualcomm EDL research, part 1
- Guanxing / hhj4ck: full-chain exploit of an unfused Qualcomm device
- Android Generic Bootloader (GBL) README
- Android Generic Boot Loader presentation slides
This article keeps the most sensitive step-by-step implementation details at a high level. The goal is to explain the architecture clearly without turning the post into an abuse guide.
Prepared for publication by GSM Alphabet and branded for alephgsm.com,
thanks from [道可道official]