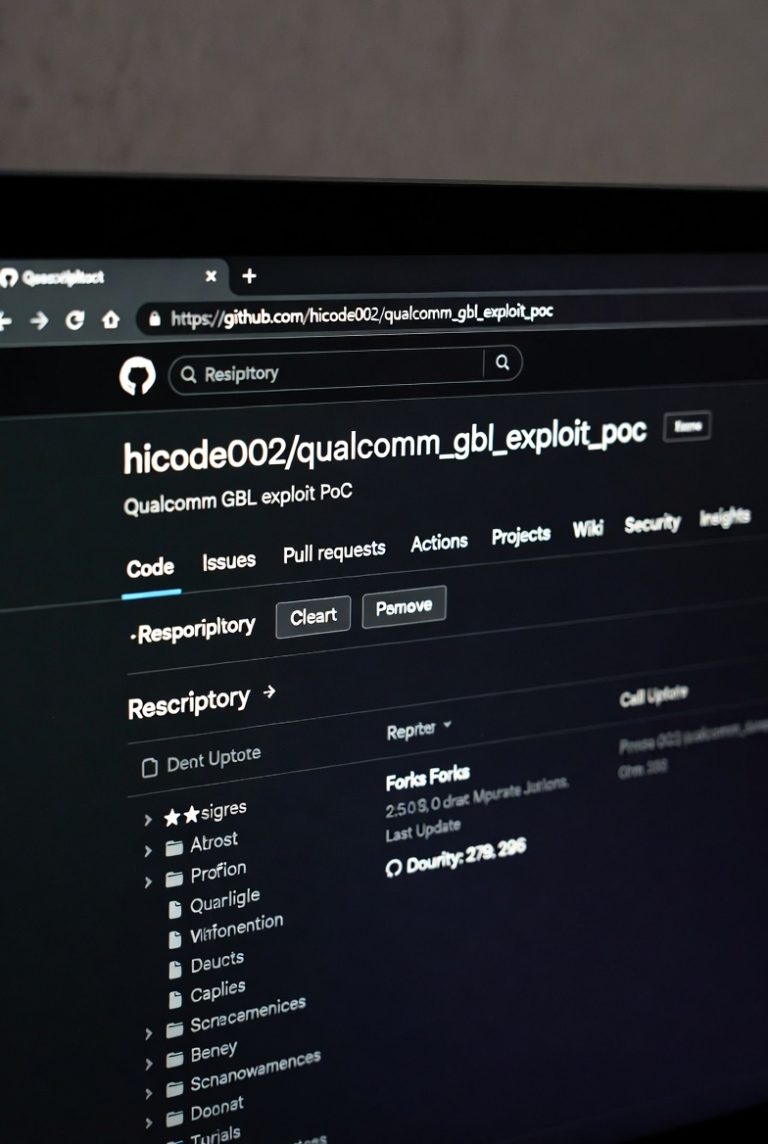
A recent research project published on GitHub — qualcomm_gbl_exploit_poc — demonstrates a proof-of-concept exploit targeting the GBL (Generic Bootloader) stage on certain Qualcomm-based devices.
The exploit works by loading a custom EFI payload and writing it into the device’s EFISP partition through a system service call. If successful, this modification can change the bootloader state and allow the device to be recognized as bootloader unlocked.
The payload used in this method is:
gbl_efi_unlock.efi Download Here
This file must be uploaded to the device manually before running the commands.
More technical discussion about the exploit can be found in the repository issue thread:
https://github.com/hicode002/qualcomm_gbl_exploit_poc/issues/5
Tested Devices
This method has been tested on the following devices:
-
Xiaomi 17
-
Xiaomi 17 Pro
-
Xiaomi 17 Pro Max
-
Xiaomi 17 Ultra
-
Redmi K90 Pro Max
Bootloader Unlock Steps
-
Reboot the device to fastboot mode.
adb reboot bootloader
-
Set the required boot parameter.
fastboot oem set-gpu-preemption-value 0 androidboot.selinux=permissive
-
Continue booting the device.
fastboot continue
-
Upload the EFI payload to the device.
adb push D:\unlock\data\mqsas\gbl_efi_unlock.efi /data/local/tmp
-
Execute the service call that writes the payload to the EFISP partition.
adb shell service call miui.mqsas.IMQSNative 21 i32 1 s16 “dd” i32 1 s16 ‘if=/data/local/tmp/gbl_efi_unlock.efi of=/dev/block/by-name/efisp’ s16 ‘/data/mqsas/log.txt’ i32 60
-
Reboot again to fastboot.
adb reboot bootloader
-
Check bootloader status.
fastboot getvar unlocked
-
Remove the EFISP payload.
fastboot erase efips
-
Reboot the device.
fastboot reboot
⚠️ This method is intended for research and testing purposes. Running exploit-based tools can potentially brick the device or cause data loss, so it should only be tested on devices prepared for development or experimentation.