C# MTK Client Source Code for Windows
SharpMTKClient is a professional C# MTK client source code project with a Windows GUI, developed by the Alephgsm team for MediaTek / MTK chipset devices.
This C# MTK client source code is designed for software owners, developers, research teams and service-tool builders who need their own private MTK protocol software instead of depending on a closed binary tool.
SharpMTKClient includes development paths for BROM / Preloader communication, Download Agent workflows, LEGACY, XFLASH and MTK V6 XML protocols, firmware flashing, partition management, file-system access, NV / IMEI logic, RPMB operations, hardware key reading and advanced patch / service workflows.
The USB protocol layer is based on Windows APIs such as kernel32. There is no UsbDk dependency. Libusb is used only for selected ControlTransfer paths where required by specific workflows.
The project has been tested across many MediaTek devices and brands, including Xiaomi, OPPO, Samsung, Huawei, Vivo, Infinix, Tecno, Itel, Motorola, TCL and other supported targets. Feature availability always depends on chipset, boot mode, selected DA, firmware package, security state and operation type.
C# MTK Client Source Code Positioning
- Product type: Commercial C# MTK client source code package
- Language: C# / .NET
- Platform: Windows
- Protocols: LEGACY, XFLASH, XML / MTK V6
- Audience: Developers, researchers and software owners
SharpMTKClient is not only a compiled end-user repair tool. It is a C# MTK client source code foundation for building, branding, customizing and extending private MTK service software.
Protocol Support
- LEGACY – Classic DA-based MediaTek workflow for supported legacy devices.
- XFLASH – Modern DA workflow with native flash and partition operations where supported.
- XML / MTK V6 – XML command workflow for supported MTK V6 firmware packages and device modes.
Protocol support depends on chipset, selected Download Agent, boot mode, storage type, firmware package and target operation.
C# MTK Client Source Code Features
- Auto-detect MediaTek devices by VID / PID.
- USB plug / unplug event handling without busy waiting loops.
- BROM and Preloader communication workflows.
- Device type support for LEGACY, XFLASH and XML workflows.
- Support paths for EMMC, UFS and NAND where DA and protocol allow it.
- Auto SLA / DAA handling paths where supported.
- Preloader crash / boot preparation paths where supported.
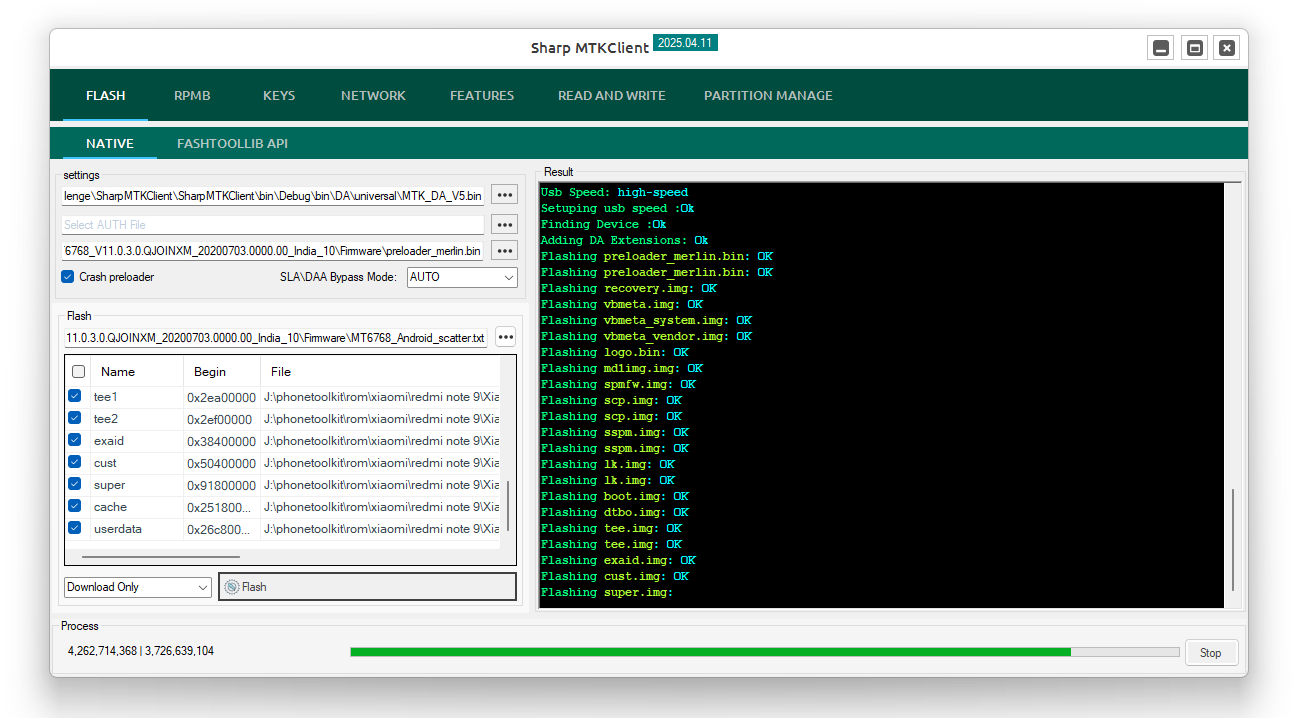
- MTKV5 and MTKV6 firmware flashing.
- Scatter firmware workflow.
- MTK V6
flash.xmlworkflow. - Native XML firmware write paths: download, firmware upgrade and download-only.
- Flash partition by name for XML and XFLASH workflows.
- Flash raw firmware.
- Raw and sparse image handling from device or file.
- Read Oxygen Forensics Detective dump paths where supported.
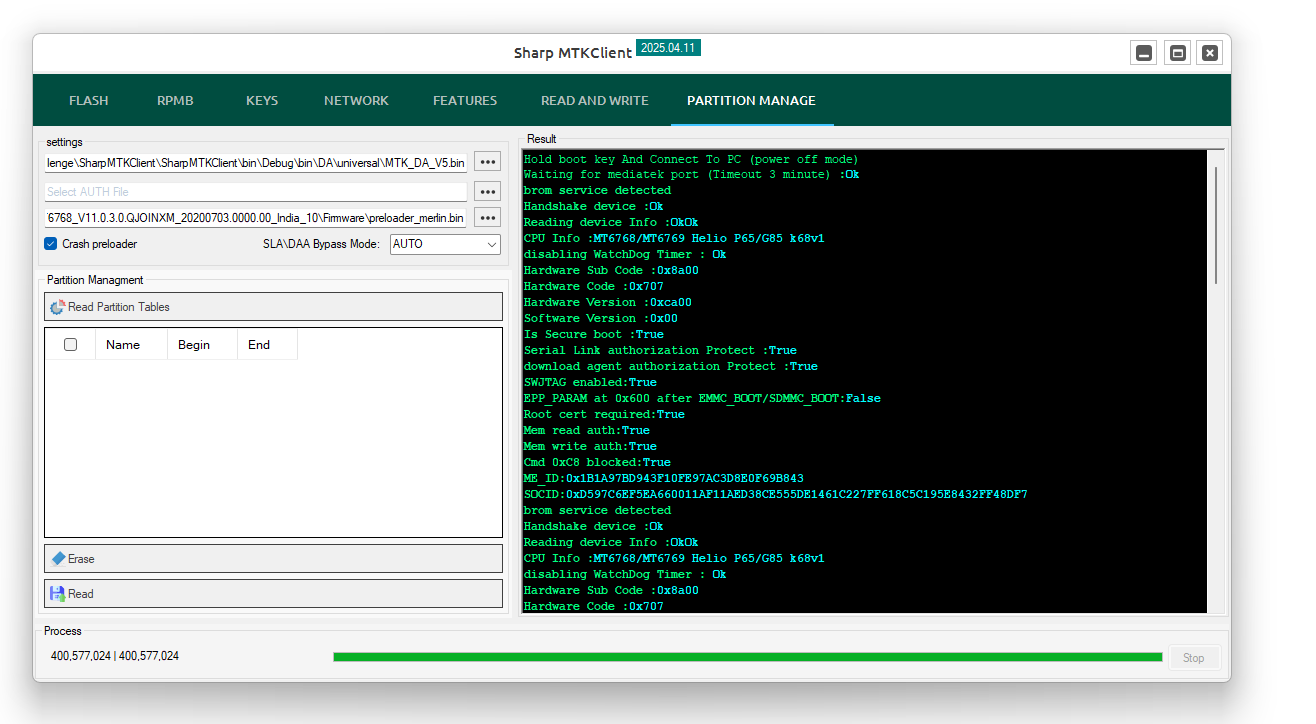
- Read GPT / partition table.
- Flash GPT.
- Rebuild GPT.
- Dump / backup partitions.
- Read selected partitions.
- Write selected partitions.
- Erase selected partitions by name or sector.
- Read preloader.
- Flash preloader.
- Safe format workflow.
- Manual format workflow.
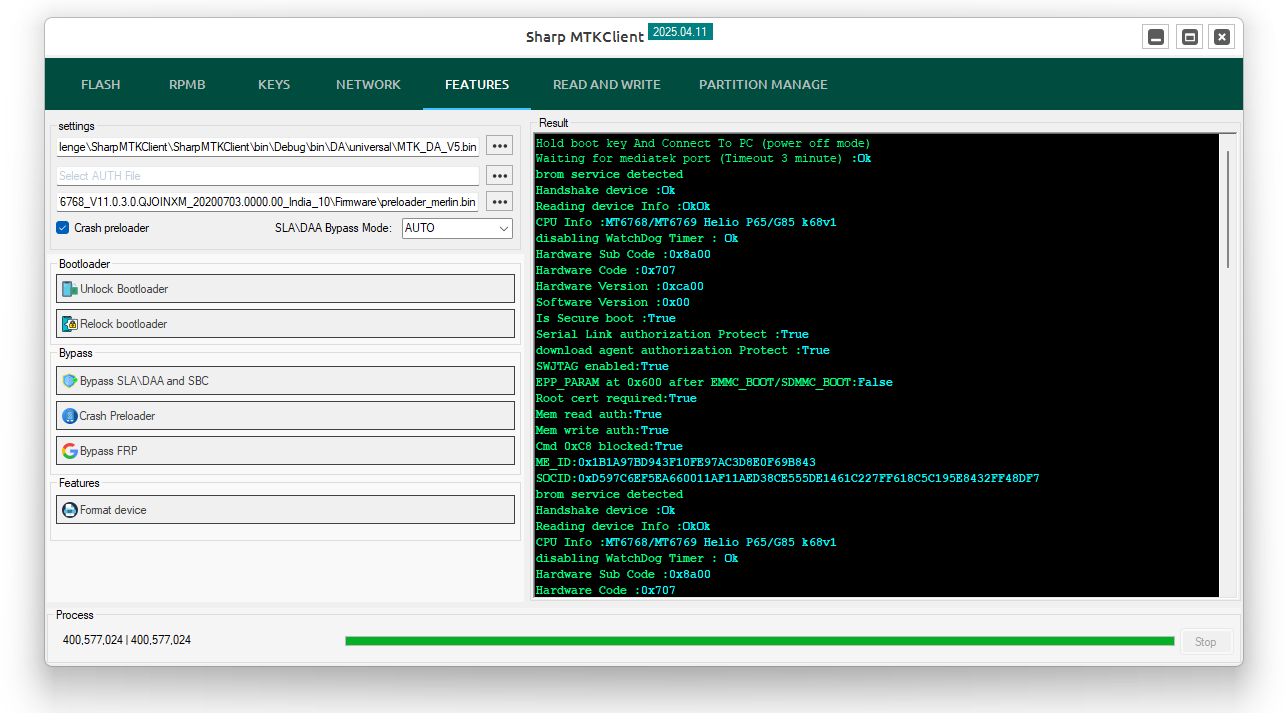
- FRP erase / reset workflow.
- Backup, write and erase NV partitions.
- Bootloader unlock and relock paths.
- Permanent bootloader unlock paths where supported.
- Fix read / orange state after bootloader unlock.
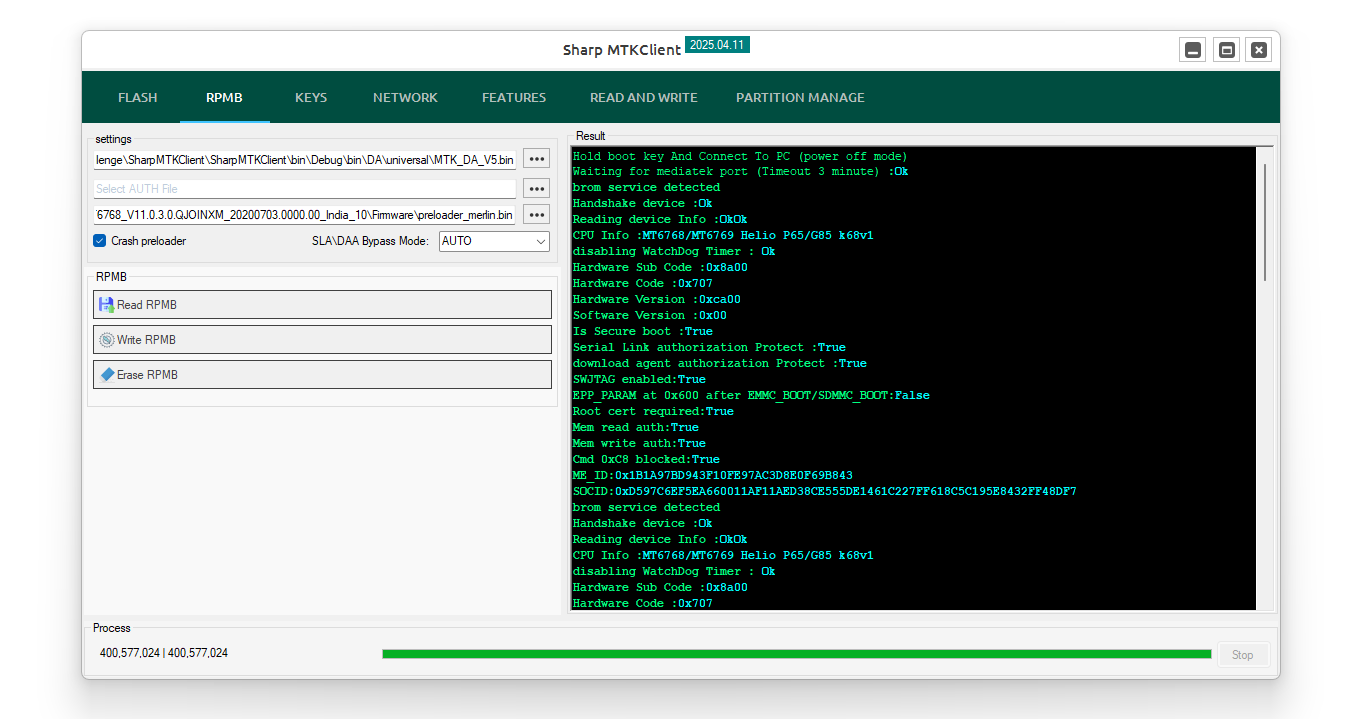
- RPMB read, write and erase paths.
- RPMB key read paths where supported.
- Hardware key read paths.
- DA parser and Preloader parser.
- Device information and Android OS information reading.
- Android
build.propparser from supported partitions.
File-System and Partition Explorer Features
- Partition explorer for EXT4, EROFS and F2FS readable partitions.
- Native C# EXT4 stream reader and writer paths.
- Mount EXT4 partitions and list files / directories with details such as modified date, UID and GID.
- Logical partition and
super.imgmetadata handling. - Browse EXT4 items from logical partitions inside
super.img. - Extract and dump files or directories from EXT4 partitions.
- Replace files inside EXT4 partitions where supported.
- Delete files from EXT4 partitions where supported.
- Add new files to EXT4 partitions where supported.
- Rename readable partition file items where supported.
- Copy readable partition files to local storage.
- EROFS detection and read paths.
- F2FS detection and read paths.
- Android information extraction from supported system / super partitions.
Advanced Patch and Service Features
- Patch certificate workflows.
- IMEI information read from device paths such as
nvdataandld0b. - Decrypt NV items.
- IMEI repair for IMEI1 / IMEI2 in FlashMode where supported.
- IMEI repair workflow areas for selected Vivo, Xiaomi, OPPO, Infinix, Tecno and Itel targets.
- Universal and Samsung MT67xx IMEI-related paths where supported.
- Remove Payjoy.
- Payjoy Remove through selected
oeminfopaths. - IT Admin / Network / Payjoy Unlock.
- Reset Huawei ID.
- Reset OPPO ID.
- Disable Mi Account through supported system, APK and hosts methods.
- Mi Account + Global through selected
cust/opcustpaths. - Mi Account Remove + Convert Global V2.
- OTA Remove for OPPO, Realme and OnePlus.
- Xiaomi OTA Remove.
- MDM + OTA Remove.
- MDM Remove.
- MDM / Walock Remove for Walton.
- SIM Lock / MDM Remove for Nothing / CMF.
- Xiaomi anti-relock Modem Patch.
- Persist Patch.
- Demo Remove.
- Restore Vbmeta for Security ON paths.
- Vbmeta Patch V1 / V2 / V3 for Security OFF paths.
- Fix no efuse state.
- Fix DM corrupted.
- Remove security plugin.
Security and Research-Oriented Paths
- SLA / DAA handling paths where supported.
- Kamakiri workflow paths where supported.
- HeapBait workflow paths where supported.
- Carbonara workflow paths where supported.
- New SLA key handling for selected Motorola, Xiaomi and AOT paths.
- Selected DA + exploit paths for supported Infinix chipsets.
- Vbmeta / dm-verity patch paths where supported.
- Brand and model-specific workflow examples where included by package scope.
Latest Updates
- Synced and improved key protocol handling across recent device workflows.
- Added basic SSR crypto integration with optional Universal Config enablement and manual
ssr_baseentry. - Added SSR key generation paths to Read Keys for RPMB, RPMB2, FDE and Motorola keys where supported.
- Updated XML and XFLASH response handling, including DA log message processing and stricter command-end error reporting.
- Reworked DA2 patching logic toward string-based function discovery for newer MTK DA2 payloads.
- Added Motorola / lamu SLA handling and improved SLA / DL forbidden error reporting.
- Updated MTK chip configuration data, including MT6880 / MT6890 modem, MT6878, MT6583 and selected legacy targets.
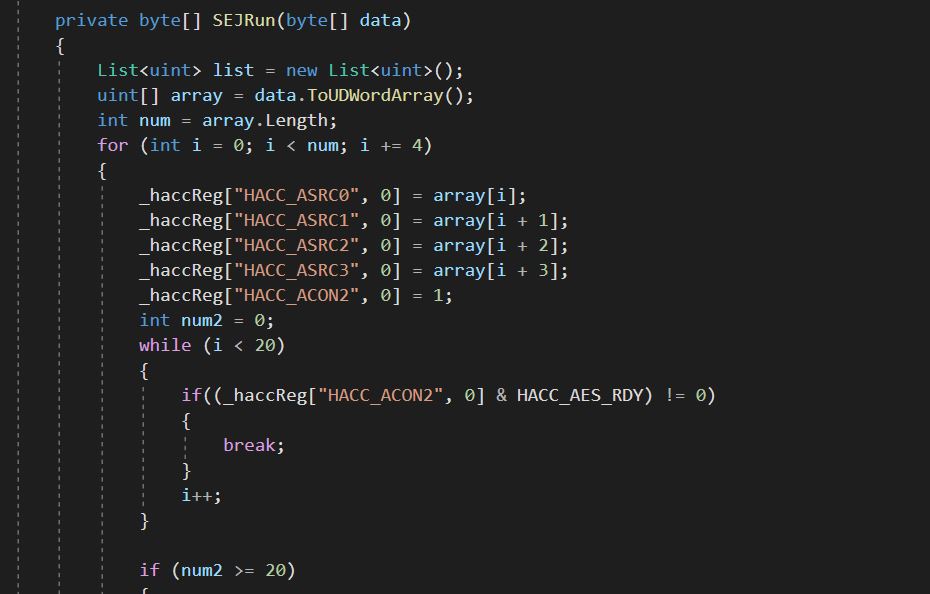
- Improved SEJ V3 hardware-code coverage and renamed updated HACC security-init register mappings.
- Improved HeapBait pointer-auth handling and ARM / AArch64 helper detection.
- Added safer GPT and partition-name handling to prevent null-name lookup failures.
- Added runtime log-channel selection support for UART, USB and combined DA logging paths.
2026.02.21
- Added patch cert.
- Added IMEI Repair for selected Vivo, Xiaomi, OPPO, Infinix, Tecno and Itel targets.
- Added remove Payjoy.
- Added reset Huawei ID.
- Added reset OPPO ID.
- Added fix no efuse state.
- Added fix DM corrupted.
- Added remove security plugin.
- Added OTA Remove for OPPO, Realme and OnePlus.
- Added Xiaomi OTA Remove.
- Added MDM + OTA Remove.
- Added MDM / Walock Remove for Walton.
- Added SIM Lock / MDM Remove for Nothing / CMF.
- Added Xiaomi anti-relock Modem Patch.
- Added Persist Patch.
- Added Demo Remove.
- Added Payjoy Remove through selected
oeminfopaths. - Added IT Admin / Network / Payjoy Unlock.
- Added Restore Vbmeta for Security ON paths.
- Added Vbmeta Patch V1 / V2 / V3 for Security OFF paths.
- Added Mi Account + Global through selected
cust/opcustpaths. - Added Mi Account Remove + Convert Global V2.
- Updated HeapBait protocol.
- Optimized protocol.
2026.02.13
- Added read IMEI info from device in all operations from
nvdataandld0b. - Added decrypt NV items.
- Added IMEI repair for IMEI1 / IMEI2 in FlashMode.
- Added universal and Samsung MT67xx key paths where supported.
- Added Mi Account disable paths through system, APK and hosts methods.
- Added permanent bootloader unlock.
2026.02.10
- Added HeapBait exploit workflow.
- Added selected Infinix chipset support paths for DA + exploit workflows.
- Added new key paths for Motorola, Xiaomi and AOT.
- Optimized code and fixed XML protocol issues.
Selected Infinix chipset support paths:
MT6789
MT6835
MT6855
MT6878
MT6886
MT6893
MT6895
MT6896
MT6897
MT6983
MT6985
MT6989
MT69932025.12.25
Watch partition explorer demonstration on YouTube
- Added partition explorer for EROFS, F2FS and EXT4FS.
- Updated EROFS algorithm.
- Added rename, replace, delete and copy-to-local workflows inside readable partitions.
- Updated additional protocol areas.
2025.10.27
- Added EROFS partition support paths.
- Added F2FS partition support paths.
- Added raw and sparse image handling from device and file.
- Optimized and fixed protocol issues.
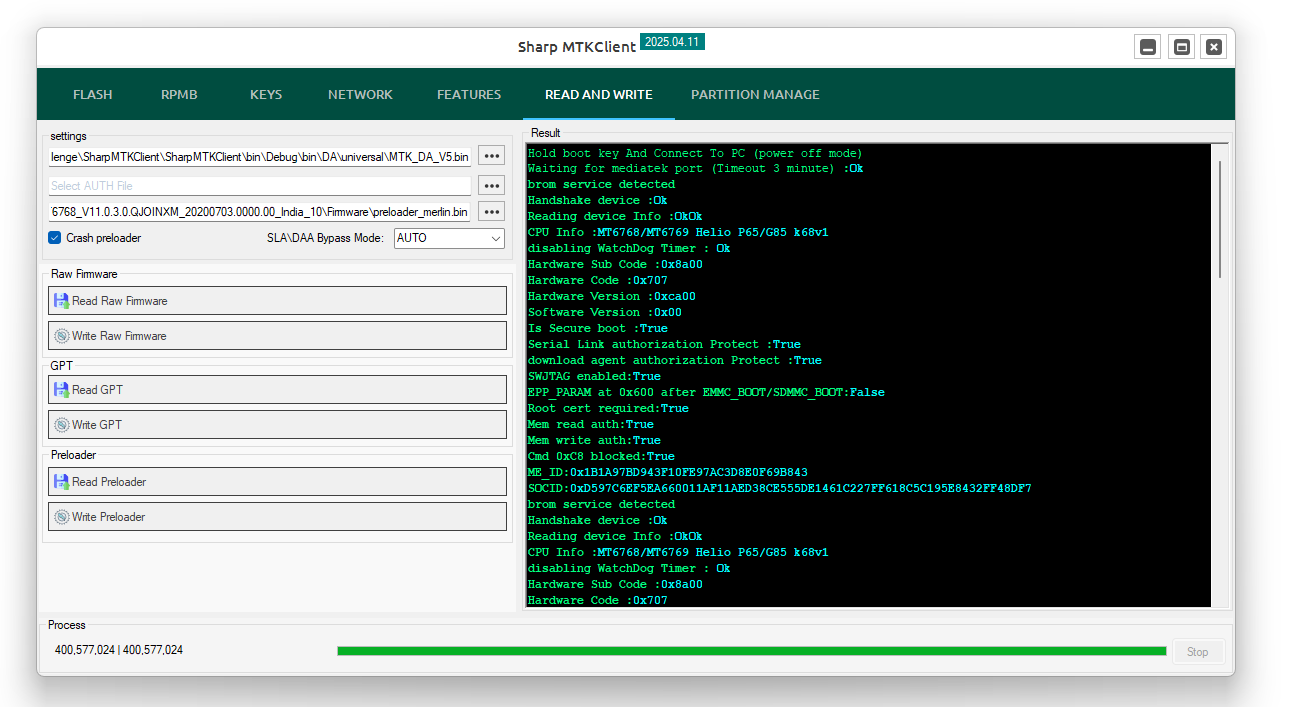
Example operation log:
Hold boot key And Connect To PC (power off mode)
Waiting for mediatek port (Timeout 3 minute) : Ok
BROM service detected
Handshake device : Ok
Reading device Info : Ok
Mediatek XFlash Detected
CPU Info : MT6768/MT6769 MT6768 (Helio G70/G80/G85)
Disabling WatchDog Timer : Ok
Hardware Sub Code : 0x8a00
Hardware Code : 0x707
Hardware Version : 0xca00
Software Version : 0x00
Is Secure boot : True
Serial Link authorization Protect : True
Download agent authorization Protect : True
ME_ID : 0x1B1A97BD943F10FE97AC3D8E0F69B843
SOCID : 0xD597C6EF5EA660011AF11AED38CE555DE1461C227FF618C5C195E8432FF48DF7
Sending payload : Ok
Trying disable SLA / DAA Kamakiri : Ok
Reading Preloader from device : Ok
Choosing the right DA : Ok
Receiving EMI : Ok
Writing download agent : Ok
Jumping Download Agent : Ok
Sync signal : Ok
Setup environment : Ok
Setup param : Ok
Connection Status : BROM mode
Sending EMI : Ok
Uploading stage 2 : Ok
Reading Partition Information tables from device : Ok
Operation : Read Partitions
Elapsed time : 00:00:582025.10.23
- Added Carbonara exploit in universal mode for selected supported devices such as Motorola G24.
- Added new keys for
handle_slapaths. - Added
build.propinformation read in supported features. - Updated MTKV6 protocol.
- Fixed and optimized multiple protocol areas.
2025.09.23
Native C# EXT4 stream reader and writer paths were added to SharpMTKClient. This implementation is written in C# and does not depend on DLL wrappers.
Watch EXT4 stream reader / writer video
- Mount EXT4 partitions and list files / directories with metadata.
- Mount logical partitions such as
super.img. - Mount EXT4 items from logical partitions.
- Extract and dump files or directories from EXT4 partitions.
- Replace files inside EXT4 partitions.
- Delete files from EXT4 partitions.
- Add new files to EXT4 partitions.
- Detect EXT4 partitions.
- Parse
build.propfrom system or super partitions.
2025.06.07
- Updated RPMB erase and write paths.
- Added vendor selection tab.
- Added selected Samsung, Motorola, Infinix, Honor, Vivo, Redmi and TCL workflow examples.
- Updated MTKV6 commands.
2025.04.12
- Added read RPMB for V6 devices.
- Added write RPMB for V6 devices.
- Added native XML firmware write paths: download, firmware upgrade and download-only.
- Added flash partition by name for XML and XFLASH workflows.
- Updated DA2 patch.
- Updated CPU list.
- Updated MTKV6 protocol.
2025.04.06
- Added native MTKV6 firmware flashing through
flash.xmland scatter. - Updated legacy protocol.
- Fixed and optimized multiple protocol areas.
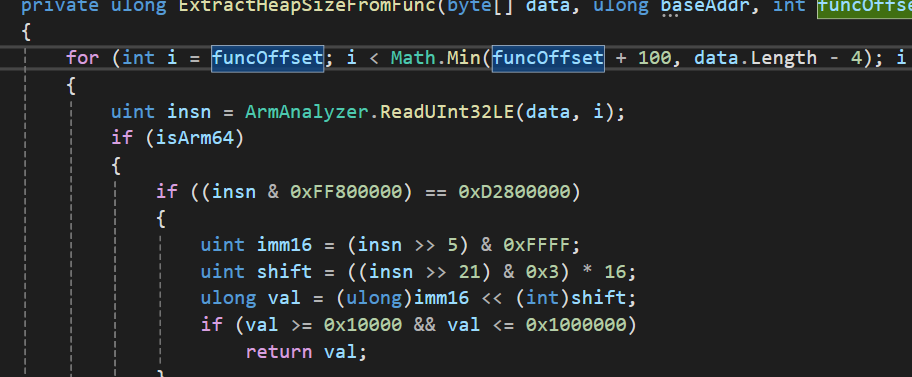
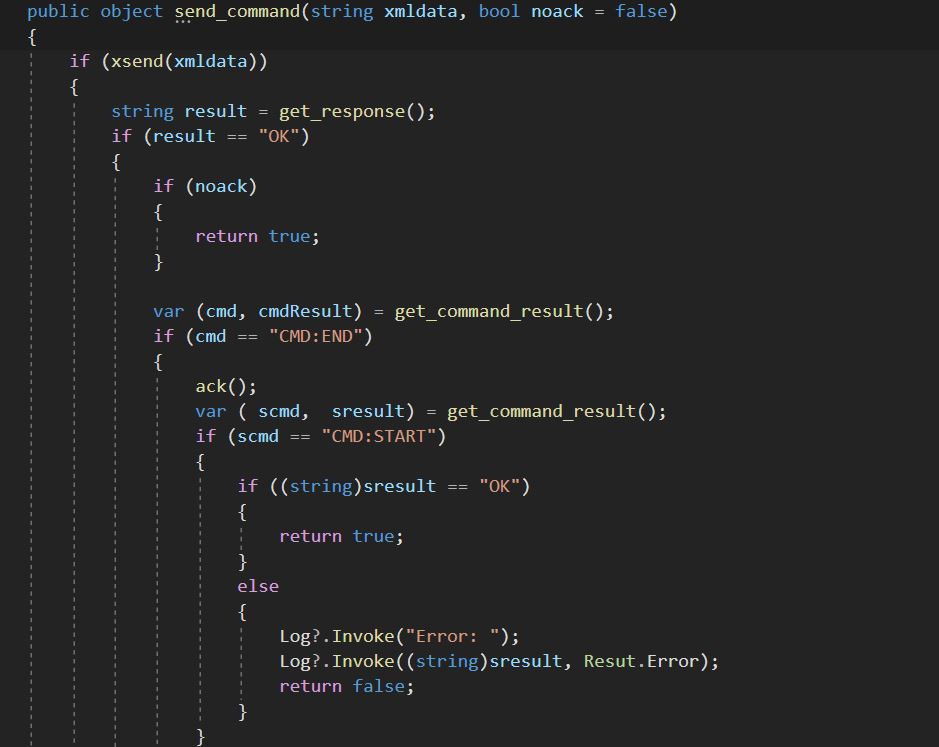
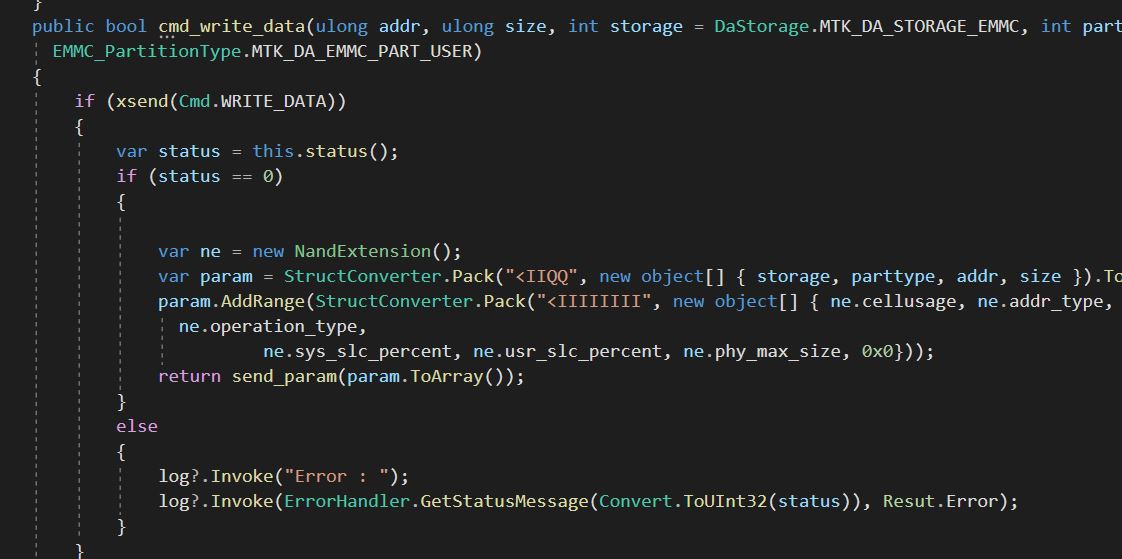
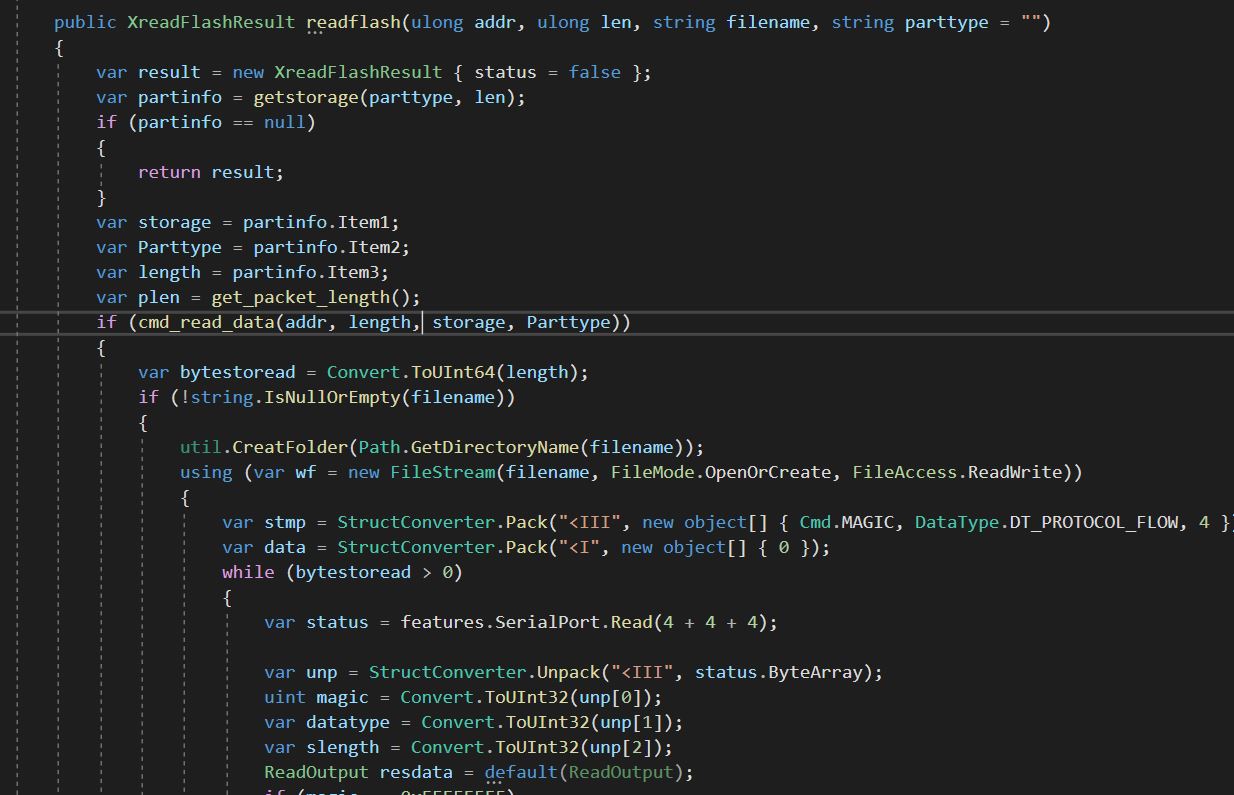
Screenshots From Code
Screenshots From Interface
Licensing and Purchase
The full SharpMTKClient source code is available through private licensing. Licensed buyers can use the source code inside their own private, internal or commercial software project according to the license agreement.
The source code must not be resold, exchanged, published for free, gifted, leaked, mirrored publicly or shared with third parties.
For pricing, licensing, support scope or technical questions, contact us on Telegram:
Product page:
https://alephgsm.com/2022/01/13/csharp-mtkclient/
GitHub Documentation
The public GitHub repository is available as a product showcase and documentation hub. It does not include the private commercial source code package.
- GitHub Repository: https://github.com/Alephgsm/SharpMTKClient
- README: https://github.com/Alephgsm/SharpMTKClient/blob/main/README.md
- Commercial License Terms: https://github.com/Alephgsm/SharpMTKClient/blob/main/LICENSE_TERMS.md
- Feature Documentation: https://github.com/Alephgsm/SharpMTKClient/blob/main/docs/FEATURES.md
- Advanced Service Features: https://github.com/Alephgsm/SharpMTKClient/blob/main/docs/ADVANCED_SERVICE_FEATURES.md
- Update History: https://github.com/Alephgsm/SharpMTKClient/blob/main/docs/UPDATE_HISTORY.md
- Media Gallery: https://github.com/Alephgsm/SharpMTKClient/blob/main/docs/MEDIA.md
- Feature Matrix: https://github.com/Alephgsm/SharpMTKClient/blob/main/docs/FEATURE_MATRIX.md
- Architecture: https://github.com/Alephgsm/SharpMTKClient/blob/main/docs/ARCHITECTURE.md
- Module Catalog: https://github.com/Alephgsm/SharpMTKClient/blob/main/docs/MODULE_CATALOG.md
- Buyer Guide: https://github.com/Alephgsm/SharpMTKClient/blob/main/docs/BUYER_GUIDE.md
- Support Policy: https://github.com/Alephgsm/SharpMTKClient/blob/main/docs/SUPPORT_POLICY.md
Disclaimer
SharpMTKClient is intended for lawful development, research, maintenance and authorized service scenarios. Device operations may depend on chipset, boot mode, selected Download Agent, firmware package, storage type, security state and local regulations.
Use this project only for authorized devices and lawful service workflows.

